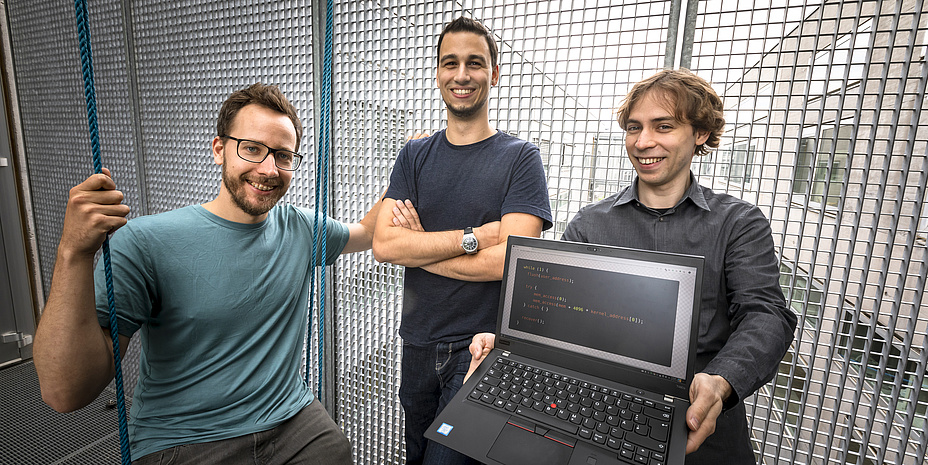
Michael Schwarz: Ideas not limited to working hours
“We don't want to see the world burning, as many people accuse us of doing,” clarifies Michael Schwarz with a laugh, over coffee in the institute kitchen. “We just want to make things safer.”
Michael Schwarz is a security researcher at the Institute of Applied Information Processing and Communications and part of the team that discovered the Meltdown and Spectre security vulnerabilities in 2017, thus opening up a completely new field of research. At that time a doctoral student under Daniel Gruss at TU Graz, he has now completed his PhD – albeit under special conditions. The contents of his thesis were still secret at the time of his thesis defence, as ZombieLoad 2.0 contained the latest security loophole which the researchers made public in November 2019 – two weeks after Schwarz graduated. “That was quite a special situation,” Schwarz admits today. They had agreed the information embargo with the processor manufacturer Intel about a year earlier. “For ethical reasons, not because we had to do it.” The researchers always report newly discovered security holes to the manufacturers first. They then have time to fix the vulnerability before the issue is published at conferences or in publications. “Otherwise we would put users at high risk because everyone could exploit the method of attack.”
The Press releases on Meltdown und Spectre sowie ZombieLoad can be found on TU Graz´ website.
In recent months, Schwarz and his colleagues have often been accused of “simply breaking things”. The 28-year-old vehemently contradicts this. “We must first learn to understand gaps in the system in order to then find a solution.” Schwarz has a lot of understanding for the manufacturers: “It's much harder to find a solution than a loophole.” For a solution, you have to consider all possible lines of attack – and that's where we want to help.”
Daniel Gruss: A passion for turning the IT world upside down.
Interested since primary school
Even at a very young age, the now 28-year-old was interested in things that were perhaps not thought about. “Others like to do crossword puzzles, I like computer problems,” he says with a grin. He laid the foundation for his current skills in primary school. Inspired by his computer-savvy father, he learned programming himself with the necessary stubbornness, since: “My father said at the time I was too young. But I was so fascinated by him typing something into the computer, which then did what he wanted it to do.”
Working time vs. free time
His fascination has not diminished since then. On the contrary. Schwarz continues to work after hours because "creative ideas are not limited to working hours. Sometimes they occur while you’re at home watching TV or in a pub having a beer”. And it was exactly the same with Meltdown and Spectre. On a Saturday evening, the trio of security enthusiasts Daniel Gruss, Moritz Lipp and Michael Schwarz met up in the Graz city centre. There was laughter, celebration and also discussions about security. “The next day, I got up and simply tried out what we had talked about the day before,” says Schwarz. “And it worked. The funny thing is, when I told Daniel and Moritz, they too were in the middle of trying it out.”
About his work, it’s no wonder Schwarz says: “I enjoy going to the office every day and before I realize it, it's suddenly evening. And although I'd like to keep working, you have to go home sometime."
The coffee is now finished. You can tell that Michael Schwarz would rather be in his office again. Admittedly, for an idealist like him, there are more exciting questions waiting there than the Planet Research interview in the institute kitchen.
This research area is anchored in the Field of Expertise “Information, Communication & Computing”, one of five strategic foci of TU Graz.
You can find more research news on Planet research. You can receive monthly updates from the world of science at Graz University of Technology via the research newsletter TU Graz research monthly.
Kontakt
Michael SCHWARZ
Dipl.-Ing. Dr.techn. BSc
Institute of Applied Information Processing and Communications
Inffeldgasse 16a
8010 Graz
Phone: +43 316 873 5537
michael.schwarz@iaik.tugraz.at